Where to Buy an Anonymous Server — Top 5 Private Solutions

In 2026, when the level of censorship and surveillance is going off the charts, the personal data of every website owner is potentially at risk. An anonymous server can be one of the solutions to protect privacy. In this article, we will explain what this solution is and how it works, where it is best to buy an anonymous server, and how to use it safely.
What an anonymous server means
From the point of view of anonymity, three main types of servers can be distinguished:
- Shared Hosting. This is the simplest and most affordable server option: tens, hundreds, and thousands of users live on one physical medium, sharing the common space among themselves. This is an economical solution, but it is fraught with anonymity issues: websites share a common hosting resource, while the hoster, meanwhile, has full access to all data.
- VPS. This is a virtual private server where each client receives their own resources. Users utilize a single server, but thanks to virtualization technologies, it is divided into isolated sections with sole control.
- Dedicated Server. The most expensive and secure solution, where the client gets a separate physical machine for their use. You do not need to share the server with anyone, and the hardware resources allow you to use the most complex encryption and traffic routing scenarios. This is a must-have solution for projects focused on maximum security.
But the level of server anonymity is affected not only by its type, but also by other criteria:
- Jurisdiction. It is very important in which country the server is registered. In the US, EU countries, and states with authoritarian regimes, data is not protected for various reasons: requests from government agencies, surveillance programs, censorship, and direct access by intelligence services. It is better to choose neutral jurisdictions — countries that are not part of military blocs, have strong trade secret laws, and instead of blindly complying with foreign warrants, require full-fledged local judicial processes to disclose data. Good examples of such states are Switzerland, Iceland, Panama, and the Seychelles.
- Logging policy. Logs are text files that automatically record user actions and general server operation. They are needed for diagnosing failures, analyzing traffic, and ensuring security, but at the same time, they compromise anonymity. Accordingly, a no-logs policy implies that the server does not record, store, or transfer to third parties information about user actions, their IP addresses, visited websites, or session times. This ensures maximum user privacy and anonymity, as the request history cannot be restored. You can verify the hosting by studying the provider's privacy policy, independent reviews, and audits. It is important that the No Logs policy is legally binding (enshrined in the terms of service or the legislation of the provider's jurisdiction), and not just a marketing promise on the website.
- Payment methods. The best scenario for maintaining anonymity is the option of transferring money via cryptocurrency. We recommend choosing the most anonymous ones like Monero and Zcash: these coins allow anonymous use by hiding transactions and other payment details from public access, which distinguishes them from Bitcoin and other popular cryptocurrencies. As another option, anonymous prepaid cards are suitable. The most reliable and anonymous payment method is cash, but it is rarely found.
- Account privacy. The following points are important for you: the ability to register an account without KYC, the use of an anonymous email, enabling 2FA (two-factor authentication), and constantly changing passwords.
- Technical security measures. It is much harder to hack a server that has regular data encryption, uses HTTPS and SSH, has regular security updates, and has DDoS protection enabled.
Top 5 best anonymous server providers
Now that it is clear what criteria to consider when choosing an anonymous server, let's look at reliable privacy-oriented providers.
ISHosting
This provider is registered in Estonia and at the same time has a rather complex asset structure, which is also registered in several other states. It focuses on minimal data collection, does not view or have access to the content of client servers, and collects only the information necessary to provide services and comply with legal requirements.
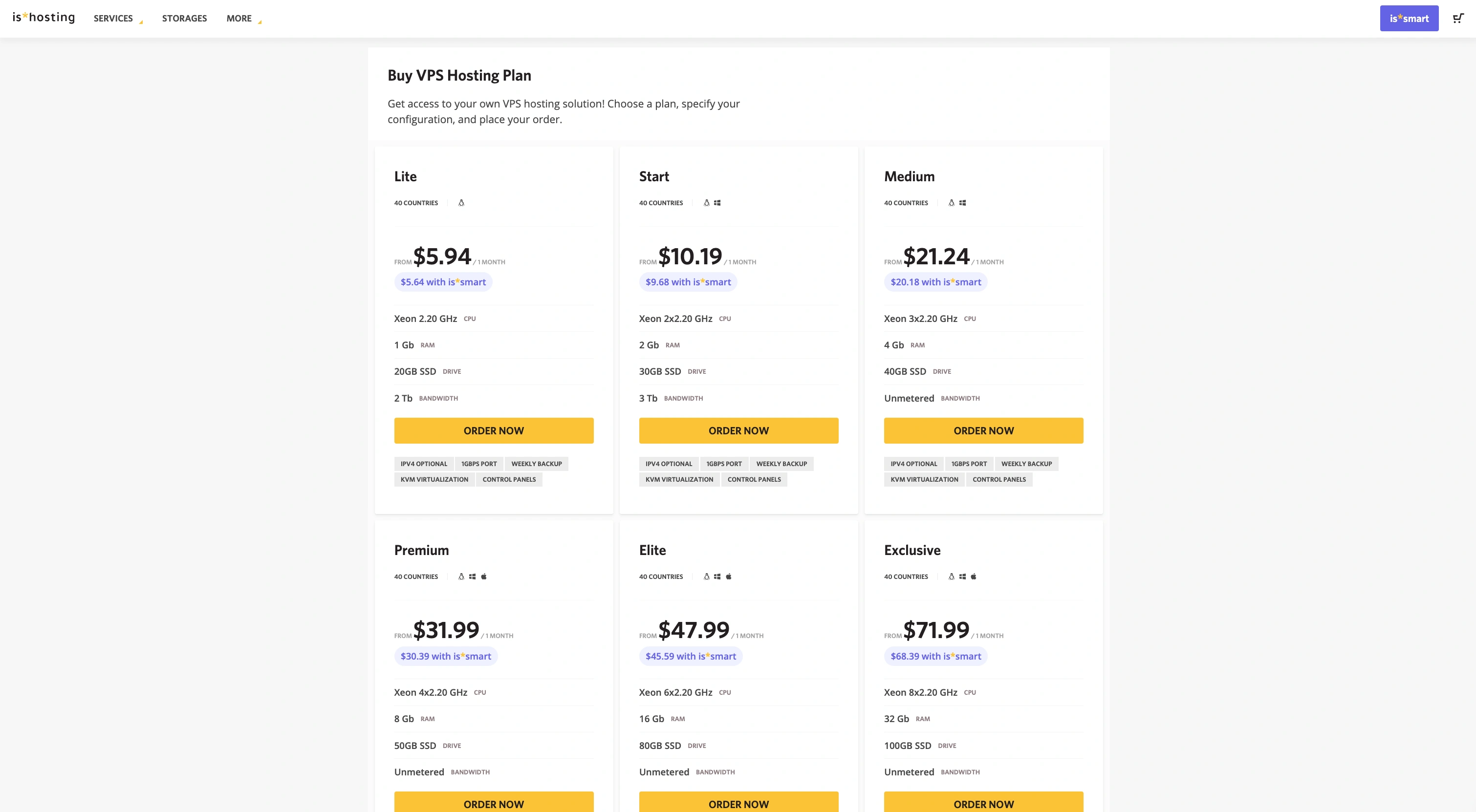
ISHosting offers clients dedicated servers in more than 40 countries around the world. Prices start at around $6 per month and go up to $70-80 when choosing exclusive plans. The hosting also provides various tools for DDoS protection, weekly backups, and round-the-clock technical support.
A big plus of ISHosting is the variety of payment methods: the provider supports payments via bank cards, cryptocurrencies, Revolut, and various electronic payment systems.
HostMeNow
This service is based in the Seychelles — an offshore zone with the most neutral and business-friendly laws. It provides the opportunity to buy an anonymous server with privacy protection right down to anonymous domain registration. KYC is not required upon registration, and the servers are located in relatively favorable jurisdictions — Finland and the Netherlands.
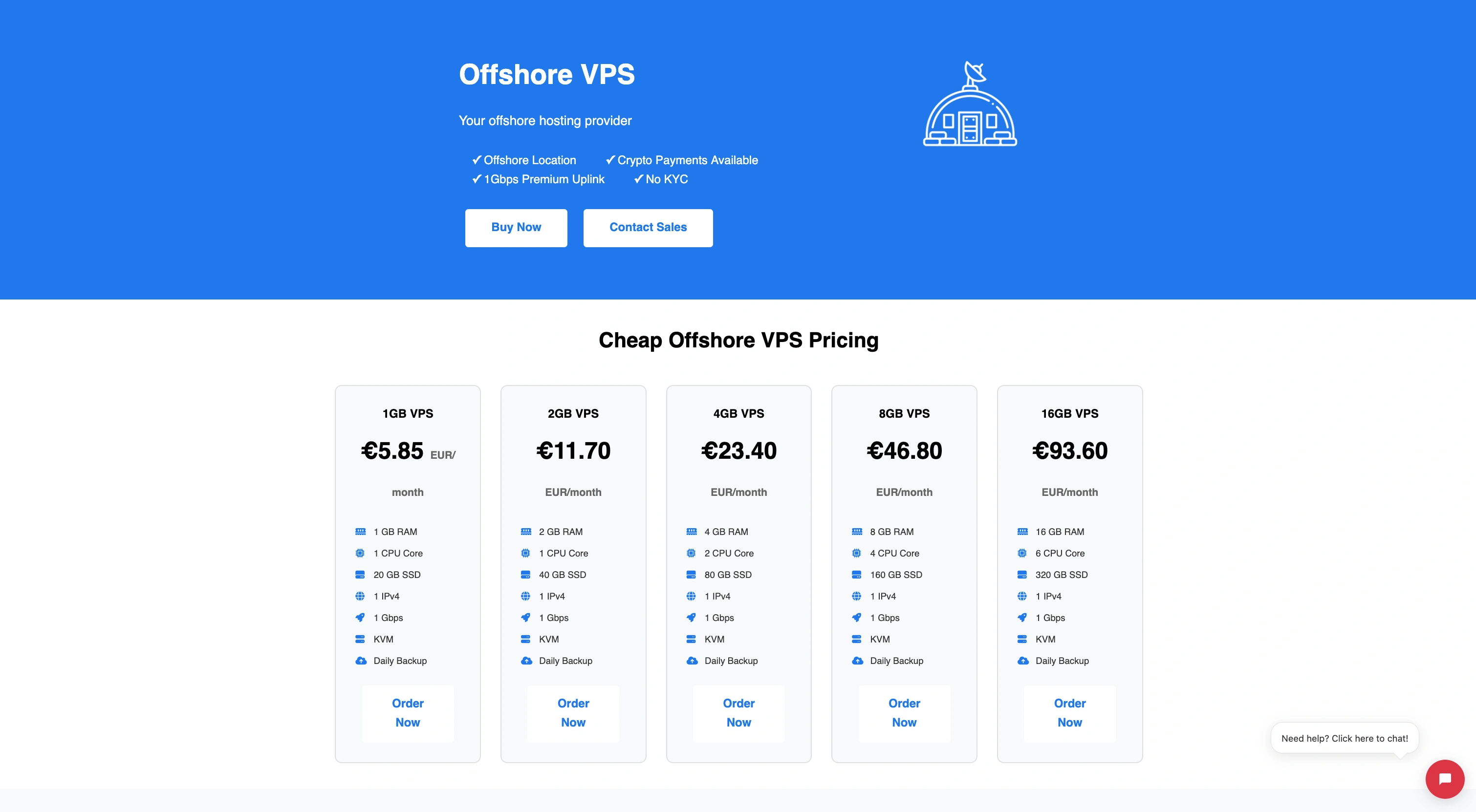
Prices on HostMeNow start at $6 for the basic version of the server. DDoS protection is included, and there is full root access and a choice of OS. You can top up your balance on the platform using both fiat methods and cryptocurrencies, including BTC and rarer coins.
FlokiNET
This company made a name for itself on privacy and freedom of speech on the internet. It appeared in 2012 and has one of the most reliable GEOs as its jurisdiction — Iceland. Only an email address is required to register on the service, and its No-Logs policy is officially declared.

The cheapest anonymous server on FlokiNET will cost 8 euros. You can choose Iceland, Finland, or Romania as its location. More expensive options can cost hundreds of euros, but DDoS protection is already included in the basic plan.
You can pay for a server on FlokiNET using popular crypto coins or even by sending money via mail.
BitLaunch
This service is registered in Panama. It adheres to a strict no-logs policy and does not use trackers. In total, BitLaunch has 27 data center locations worldwide.
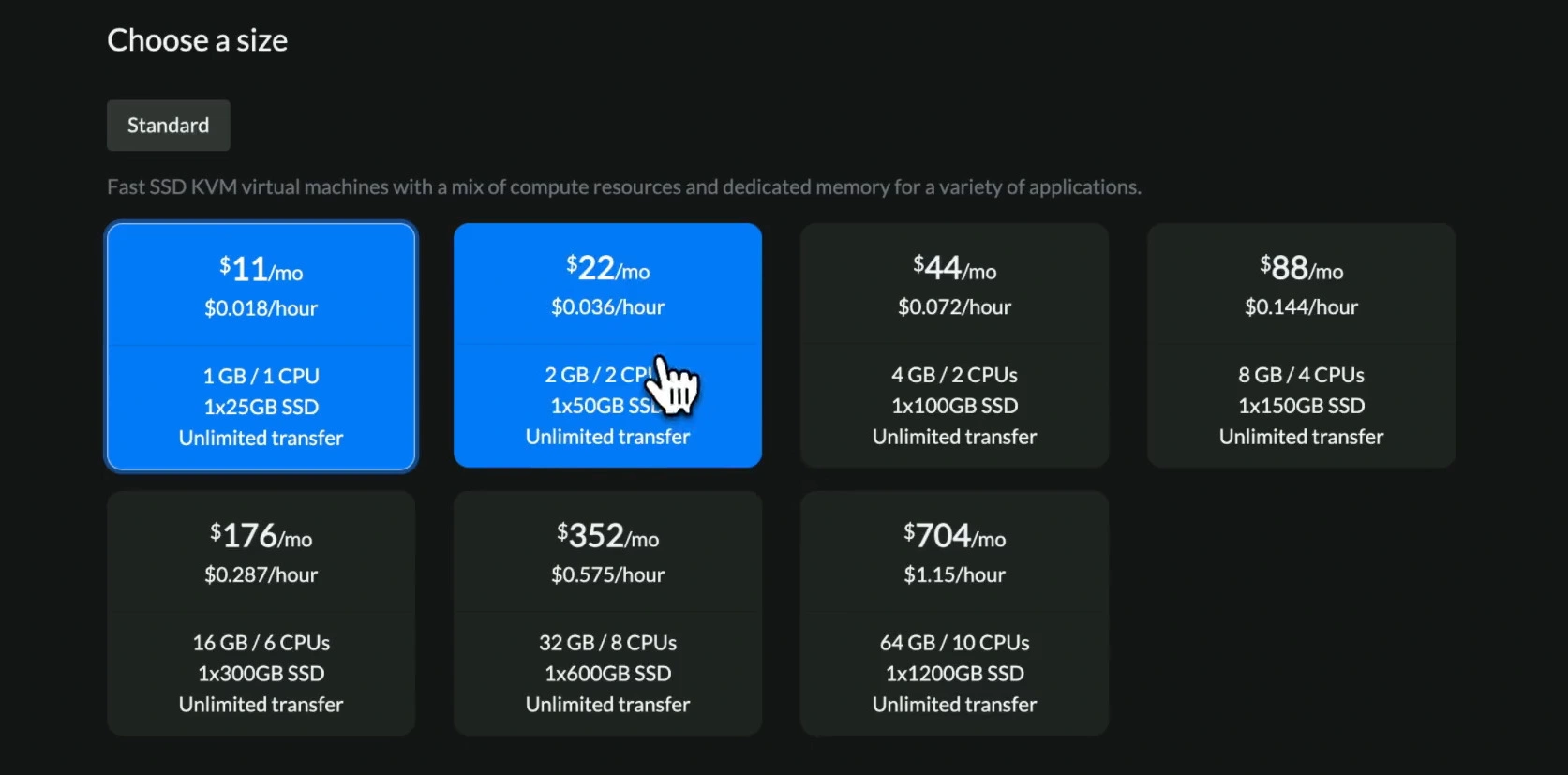
Basic BitLaunch servers will cost at least $10 per month, while the most expensive plans go up to $1400 for the same period. The service offers an hourly payment system: you top up your balance with the chosen amount and pay for each hour of VPS usage. The platform accepts payment for its services only in cryptocurrency, which is especially valuable from an anonymity standpoint. There is also a trial period, the duration of which is determined by a technical support manager.
PrivateAlps
This is a premium service from Switzerland, tailored for maximum client privacy. It offers bulletproof servers with an administration service if the client lacks the relevant skills. PrivateAlps prohibits hosting websites that explicitly violate the law (weapons, child pornography, etc.); otherwise, buyers are guaranteed absolute anonymity in accordance with the No-Logs policy.
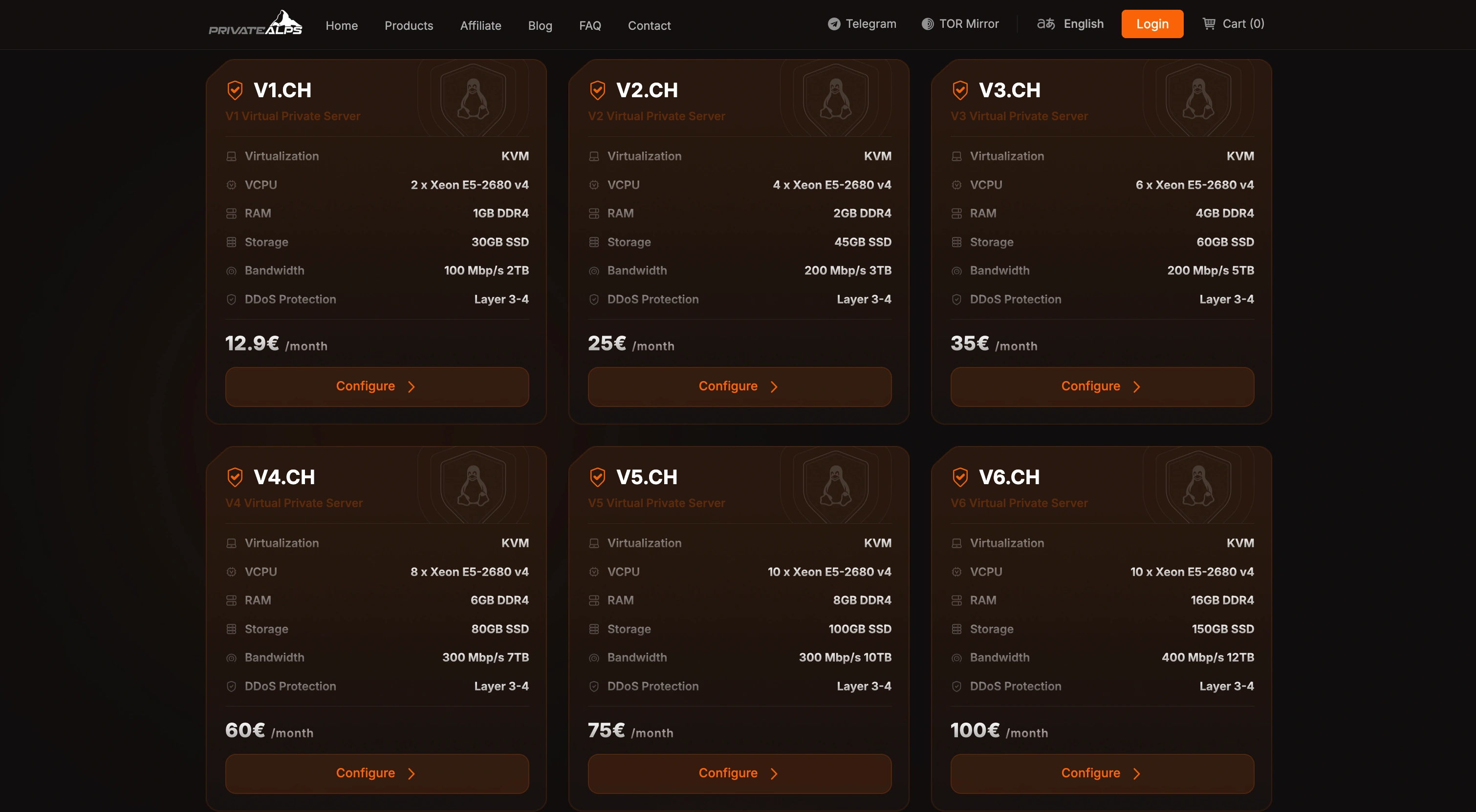
PrivateAlps plans start at 13 euros per month. The service provides various service packages at the client's discretion, and all its data centers are located in Switzerland. Top-up transactions are accepted in Bitcoin, Litecoin, Monero, and other cryptocurrencies.
How to safely use an anonymous server
It is not enough to simply rent anonymous hosting; you need to know how to use it correctly to maintain anonymity. Additional recommendations include:
- Using TOR and VPN. Even if the server itself does not keep logs, your internet service provider sees that you are connecting to a specific IP address in a data center. This creates a direct link between your physical identity and your anonymous project. To break this link, you should always connect to the server via a VPN service with a no-logs policy or through the Tor network. In this case, the provider only sees encrypted traffic to the VPN node or the Tor entry node, but does not know exactly which server you are accessing.
- Encrypting all data. An anonymous server protects data from the hosting provider, but does not guarantee its security during transmission over the internet. Without encryption, the information you exchange with the server (logins, passwords, files) can be intercepted by malicious actors or intelligence services at intermediate nodes. Always use encrypted protocols: connect via SSH (not Telnet), configure FTP only using SFTP/FTPS, and be sure to install an SSL certificate on your website.
- Regular software updates. Vulnerabilities in older software versions are the most common cause of server hacks. If an attacker gains access to your server, they can not only steal data but also deanonymize you. Make it a rule to regularly update the operating system, control panel, and all installed applications. By configuring automatic security updates, you will protect the server from leaks, even if you do not check them manually every day.
- Monitoring server activity. Even the best protection can fail. Regularly review your server's access and error logs — there you can detect suspicious login attempts, unfamiliar IP addresses, or any other anomalous activities. Use simple monitoring tools that will alert you to unexpected CPU or traffic loads — this could be a sign that the server has been compromised.
- Creating data backups. Even an anonymous VPS will be useless if you lose the results of your work due to a technical failure, a hacker attack, or the server being blocked by the provider. Regular backups are an insurance policy that will allow you to quickly restore the project in a new location. Store copies in an encrypted form and in another secure location (for example, on a local encrypted drive or with another anonymous provider) to maintain access to information even in an emergency situation.
Conclusion
An anonymous server is just the first step towards digital freedom: it is important not only to find a provider with a convenient jurisdiction but also to follow basic rules of digital hygiene when working with it. Security is made up of many details, from the payment method to regular software updates, and only a comprehensive approach guarantees data safety. Use the recommendations presented in the article and choose a private solution wisely to maintain your own privacy in any unforeseen circumstances.
Frequently Asked Questions
Yes, using an anonymous server is legal in the vast majority of countries worldwide and is considered a tool for protecting privacy and data confidentiality. Legal issues can only arise from your actions: if you use the server to host prohibited content or commit illegal acts, anonymity does not exempt you from liability.
Countries with strong data protection laws that do not participate in international information-sharing agreements are considered optimal: Iceland, Switzerland, Panama, and the Seychelles. These jurisdictions do not require the automatic disclosure of client data upon foreign requests and often legally restrict the application of the DMCA (the US copyright law).
KYC (Know Your Customer) is a client identification procedure where the provider requires passport details, proof of address, and other personal information when purchasing their services. The absence of KYC is critical for anonymity, as without it, no legally significant link is created between your real identity and the server: the provider will simply have nothing to show, even upon request from the authorities.
Absolutely, otherwise your ISP will see a direct connection to the server and will be able to link your identity to the project. A VPN and Tor create an additional layer of protection: the ISP only sees encrypted traffic going to an intermediate node, but does not know exactly which server you are accessing, which breaks the identification chain.
You bear full legal responsibility for all content and actions committed from your server, regardless of its level of anonymity. Anonymity does not equal impunity: law enforcement agencies can use various methods to establish the identity of the server owner when it comes to serious offenses.

