Why IP Cleanliness is Important and How to Check It?

The cleanliness of an IP address is critically important if you need unimpeded access to web resources, no risk of blocks, and successful delivery of email campaigns. In today's article, we will break down what clean IPs are, what parameters can be used to check their reputation, and which addresses should not be used to avoid falling under the anti-fraud filter.
What is a "clean" IP and why is it important
A clean IP is an address with a positive reputation on the network, which is absent from spam lists and has not been used for fraudulent activities.
Any clean IP addresses will meet several criteria:
- Absence from blacklists (DNSBL, RBL). This is the basic level of digital hygiene. If an IP becomes dirty, it usually ends up in public blacklists (Spamhaus, Barracuda, etc.). This is the main sign that the address was used for sending spam and other malicious activity.
- Low Fraud Score / Reputation Score. Anti-fraud platforms (e.g., Scamalytics, IPQS, MaxMind) assign a risk score to each address. A clean IP has a minimal score, close to zero, which means a high degree of trust in it.
- No history of abuse. Not only the current state is important, but also the past of the address. If phishing attacks, brute force, or spamming were previously recorded from this IP, its reputation will be considered questionable even after a change of owner.
- Correct geolocation and ASN. A clean IP must correspond to the address declared by the ISP. If, for example, checkers show that the address belongs to a provider in Germany, but the geolocation floats between the Netherlands and Russia, this is a serious signal for anti-fraud systems.
- No connection to proxies, VPNs, and data centers. An ideal address should not be detected as a VPN, Tor node, public proxy, or data center server—otherwise, the cleanliness of the IP will be questioned by anti-fraud systems.
A preliminary check of the IP for cleanliness will facilitate further work:
- Passing verification on platforms. An IP address that is detected as belonging to a VPN or data center will make registration on Google, Facebook, or Amazon difficult. And even if you manage to pass verification, no one guarantees that you won't be blocked in the future.
- Bypassing captchas and other additional checks. If the IP belongs to a database of suspicious addresses, you will regularly waste time passing checks, repeatedly selecting traffic lights and fire hydrants in pictures. Clean IPs, however, do not face such obstacles.
- Stable account operation. Most bans and blocks are associated precisely with previous suspicious activity from the IP address. Clean IPs are a guarantee of a long and stable existence of an account, whether it is a profile on a crypto exchange or a Facebook account.
- Trust of anti-fraud systems. Modern anti-fraud systems work based on behavioral analysis and reputation databases. They do not just block obvious violators but also assign their own trust coefficient. A clean IP receives high trust, which allows performing sensitive actions (withdrawing funds, changing payment details, and launching advertising campaigns) without triggering additional checks.
- Email deliverability and indexing. In email marketing, IP cleanliness is critical: sending email campaigns from a spammed address might not even start, or all emails will go straight to the "Spam" folder. And for SEO specialists, a "dirty" address means constant captchas and bans of scrapers and other working tools.
Where do "dirty" IP addresses come from
Every server that has been flagged by an anti-fraud system received its "black mark" for certain negative actions. They can be divided into four main groups.
Usage history
This is the most frequent and common reason for an IP address to end up on a blacklist. Here is what can be inherited by the new owner of the server:
- spam campaigns
- phishing campaigns
- brute-force attacks
- DDoS attacks
- compromise in data leaks, etc.
AbuseIPDB, Spamhaus ZEN, haveibeenpwned and other projects providing access to databases of fraudulent IPs collect and store data for years. If an address has been spotted in untrustworthy activity, this history can no longer be erased.
Subnet type
Anti-fraud systems look not only at a specific IP but also at its surroundings—the entire subnet to which it belongs. If many violations are recorded in the range, everyone suffers. This is primarily relevant for shared proxies: if one user from the pool spams or engages in brute-forcing, the reputation of the IP address as a whole drops, including for everyone who uses it.
As for datacenter proxies, they are often detected and banned by anti-fraud systems preemptively: due to their low price, such addresses are used by spammers and scammers.
Incorrect configuration
An IP address may initially be clean, but errors in its configuration settings can lead to critical consequences. Here are the most common scenarios of proxy conflicts with platforms.
| Problem | Practical example | Risks |
|---|---|---|
| DNS leaks | DNS requests go to the servers of a provider different from the IP (e.g., the IP is from the US, but DNS requests go to Russia) | Anti-fraud sees the discrepancy and marks the traffic as a proxy |
| WebRTC leaks | The browser reveals the real local IP even when using a proxy/VPN | Disclosure of IP address spoofing |
| IPv6 leaks | The proxy is configured only for IPv4, but the system sends requests via IPv6 (where there is no protection) | Leak of real location, blocking |
| Geolocation and time zone mismatch | IP is from New York, but the system time zone is set to Moscow | Anomalous behavioral factor and subsequent ban |
| Language and region mismatch | IP is from France, but the browser language is Ukrainian | Another trigger factor for anti-fraud |
Usually, anti-fraud systems check the digital fingerprint of the device when verifying users. Any inconsistency between the IP, DNS, time zone, browser language, OS version, and other parameters lowers the trust rating, even if the IP itself is technically clean.
Automatic blocks
Even a perfectly configured IP can be "dirtied" by your own actions. Platforms track not only technical parameters but also behavioral patterns. If the behavior differs from a typical user's, the system marks the IP as suspicious.
The cleanliness of an IP is negatively affected by:
- multi-accounting. This is a red flag for any major platforms: even if technically the creation of multiple accounts by one user is not prohibited, for the system, it is a powerful trigger for verification. Account linkage is detected by identical browser fingerprints, which compromise "dirty" IPs.
- suspicious activity. Filling out a registration form in a second, clicking at identical intervals, instant transitions between pages without pauses to read content, and scrolling pages at a constant speed indicate automated behavior.
When an anti-fraud system sees such scenarios, which are atypical for a regular user, it immediately flags the account for additional verification.
Key parameters for checking IP cleanliness
Even the most reliable providers are guilty of selling addresses with a questionable history. Fortunately, you can check the cleanliness of an IP yourself.
Checking blacklists
First, we will go through public databases of "dirty" IP addresses spotted in spamming, phishing, and other abuses. There are quite a few of them on the market, and each database operates according to its own criteria.
| Name | Specifics | Importance |
|---|---|---|
| Spamhaus ZEN | A combined list, includes SBL, XBL, PBL, and is considered one of the most authoritative on the internet | Critical — if the IP is in Spamhaus, it is almost 100% "dirty" |
| Barracuda Reputation Block List | Used by many mail servers and corporate systems | High |
| SURBL | Focuses on URI spam | Medium — important for email marketing |
| AbuseIPDB | User-driven database of complaints about attacks (brute-force, scanning, DDoS) | High — reflects "fresh" activity |
| SORBS | Historically significant list, but now partially outdated | Medium |
You can check the presence of an IP in spam databases via:
- mxtoolbox.com — checks against 100+ lists, saves the history of checks
- talosintelligence.com — shows the IP reputation in the Cisco ecosystem
- dnsbl.info — a niche RBL checker.
Ideally, the IP address should not be in any of the known lists. If it does appear in one of the secondary databases, it is an alarming signal, and its presence in Spamhaus or Barracuda is a definite red flag.
Fraud Score / IP Reputation
Next, we move on to the fraud rating—this is an assessment of the probability that the IP is used for fraud, even if it is not on blacklists. The final Fraud Score is formed by many factors, including:
- IP history
- subnet type
- anomalous behavioral factors, etc.
Top services for checking the fraud rating include:
- IPQualityScore (IPQS): up to 5,000 requests per month can be made for free.
- Scamalytics: has a limited free allowance.
- IPVoid: a completely free service.
- AbuseIPDB Confidence Score: also works for free.
Checking an IP for cleanliness can yield various results—here is the generally accepted Fraud Score scale in the industry:
- 0-15 — excellent, the address can be used for any platforms
- 15-40 — risky, the probability of encountering a captcha and additional checks increases
- 40-70 — high probability of blocks, not recommended for use
- 70-100 — almost a 100% chance of blocking, the IP has a dirty history.
Ideally, it is better to check the address through different services to get a sort of averaged rating based on multiple values.
Network type and ASN
Anti-fraud systems always look at who owns the IP. Even if it is clean according to RBLs and has a low Fraud Score, its network type can be a reason for blocking. The same applies to the ASN—the autonomous system number, which is the identifier of the network to which the given address belongs.
Here are a few services that will help check the cleanliness of an IP by ASN and network type:
- ipinfo.io: shows the ASN, organization, and network type.
- IP2Location: detects data centers, proxies, VPNs, and Tor.
- Whoer.net: shows the ASN and the provider's country of registration.
- bgp.he.net: detailed information about the ASN—the owner and network ranges.
If, based on the check results, the addresses are displayed as datacenter ones, this is again a red flag: such IPs will be automatically blocked on most platforms.
Geolocation and compliance
What a typical anti-fraud system looks at:
- country — the IP must belong to the GEO where the user is located
- city — a desirable but not critical match (a difference of 50-100 kilometers is acceptable)
- time zone — must match the IP region
- provider — the ISP name must match the country and network type
The services from the previous point also check addresses for geolocation compliance with real parameters. Note: a spread in the IP location is not yet a critical issue, but a country discrepancy between the address and the user's geolocation is a clear sign of a proxy or VPN for an anti-fraud system, which may subsequently lead to a block.
Proxy / VPN / Tor detection
For platforms with strong anti-fraud systems, this is probably the most important parameter—if the address is detected as a proxy, even the cleanliness of the IP will not help.
It is important for us to find out during the check:
- whether the IP is used for a proxy server (HTTP/SOCKS)
- whether the IP is a VPN server (OpenVPN, WireGuard, etc.)
- whether the IP belongs to a Tor node (exit node)
- whether the IP is in public proxy lists
You can check the IP for cleanliness and non-compliance with address spoofing tools via:
- Pixelscan.net — a specialized tool for detecting proxies and bots, shows the user's digital fingerprint and WebRTC leaks.
- Whoer.net — VPN/proxy detection, anonymity check.
- BrowserLeaks.com — a whole set of leak tests, including WebRTC, DNS, and JavaScript.
- IPQualityScore — gives an exact answer on whether the IP belongs to a proxy, VPN, or Tor, and determines the network type.
Speed and ping
This is an indirect but important parameter that characterizes clean IPs. High ping can cast suspicion on all user traffic, and speed spikes can be identified as a sign of cheap proxies.
Check your server's connection speed via:
- Speedtest.net — download/upload speed, ping
- Ping.pe — ping from several points around the world
Based on the check results, you can evaluate the IP:
| Parameter | Good | Acceptable | Bad |
|---|---|---|---|
| Ping | <50 ms | 50-150 ms | >200 ms |
| Download speed | >50 Mbps | 10-50 Mbps | <10 Mbps |
| Upload speed | >10 Mbps | 5-10 Mbps | <5 Mbps |
Low connection speed will not always be a risk factor for anti-fraud systems. But instability indirectly indicates a connection via a proxy or VPN. In addition, it is simply inconvenient when performing work tasks on accounts.
Step-by-step guide: how to check IP cleanliness yourself
You already know how IP cleanliness is determined, which means it is time to break down in practice how you can check it step by step.
Basic check
First, you should go to 2ip.io or whoer.net. We are interested in the following parameters:
- GEO (whether it matches the one being checked)
- provider (not a data center)
- language and time zone (match the IP)
- VPN and proxy detection (not detected)
- anonymity (low — a sign of a regular user).
Obviously bad IP addresses will be eliminated at this stage.
Step 2: checking blacklists
Here, two services will be enough for us, and the first of them is abuseipdb.com. Open the site, enter the IP into the search bar, and analyze the results:
- Abuse Confidence Score — should be up to 10%
- Total Reports — the number of complaints (ideally, there should be none at all)
- Last Report Date — the date of the last complaint (an alarming signal if there were any in the last month)
- ISP / Usage Type — a home provider or mobile network, not a data center.
Next, mxtoolbox.com will help us. Check the IP address there as well, and evaluate the output:
- all lists are green — excellent, the address does not belong to any of the blacklists
- one or two yellow lists — if it is Spamhaus or Barracuda, reject the IP
- several red lists — definitely do not use this address.
Step 3: Fraud Score and reputation
To check the fraud rating, go to the Scamalytics.com website. Enter your IP and get the following data:
- Fraud Score — ideally up to 15; an IP with a score above 40 is considered "dirty"
- Risk Level — we need a low one, medium will do in some cases
- Proxy/VPN/Tor Detection — discard the IP if it fails one of these checks.
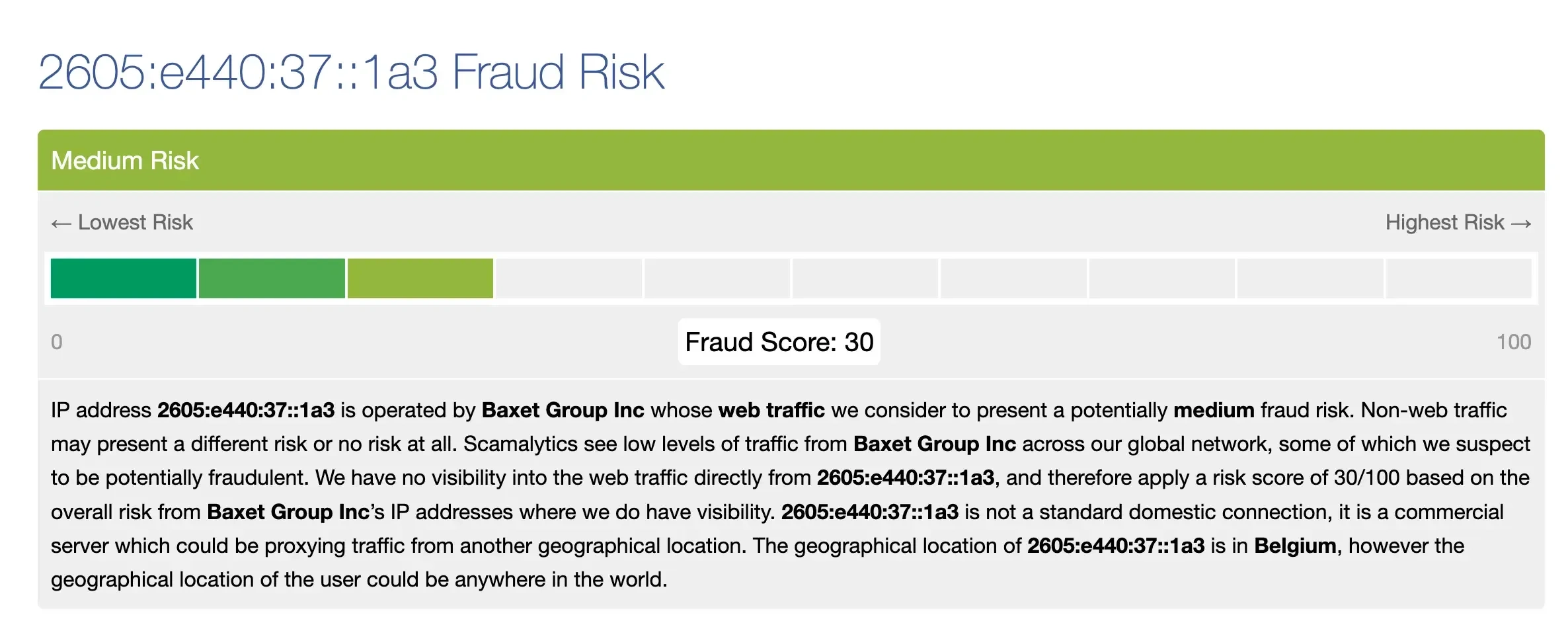
The main check in this point is, of course, the Fraud Score. For an additional check, you can go to ipqualityscore.com to see, in addition to the fraud rating, whether there have been complaints against the address in the last 30 days.
Step 4: leaks and fingerprints
By this point in the list, completely clean IPs will remain, but it is worth making sure that they lack any technical problems. Checking through the following services will help us:
- BrowserLeaks.com checks for WebRTC leaks revealing the real IP address, the match of the visible IP with the checked one, DNS leaks, and the browser fingerprint as a whole. Failing the check on at least one of these parameters is a reason to change the address.
- dnsleaktest.com shows DNS leaks. We will be satisfied with a result where only the DNS servers of the IP's country are shown. If they belong to another GEO, for example, the one where you are physically located, there are leaks, and the real address is revealed.
- pixelscan.net — a comprehensive anonymity check. The scan lasts 10-20 seconds and identifies all possible problems that will complicate further work with this IP. Pay special attention to markers for bots, proxies, VPNs, and data centers. The tool also shows the IP reputation—if it determines it to be low, it is better to change the connection.
Step 5: checking on specific platforms
The final step is checking the IP in action:
- Open the platform you plan to work with (Gmail, Facebook, Binance, etc.).
- Try to create a new account.
- Evaluate the result using the table below.
| Observation | Evaluation |
|---|---|
| Registration went through without issues | The IP successfully passed the check |
| Phone / email requested for verification | Normal for many platforms, but if the request happens constantly on different accounts, it is already suspicious |
| Captcha (reCAPTCHA / hCaptcha) | Once or twice is normal, but if at every step, the IP is in the gray zone |
| Ban | The IP is blocked by the platform |
When the account is successfully created, let it rest and log in after a few hours. A block in the near future will show that the IP cleanliness check was still not passed. The repeated appearance of a captcha is an alarming sign: you can work with the profile, but it is better to prepare backups right away.
Conclusion
Investing in clean IPs is not a whim, but an investment in the stability and success of your work, which will directly pay off with the safety of your accounts. The reputation of an IP can change at any moment, so regular checking should become the norm. Use the step-by-step guide from this article to test your IPs today—it will take no more than 10 minutes but will save hours on solving problems with anti-fraud systems in the future.
Frequently Asked Questions
With shared proxies, an IP's reputation can plummet in a matter of hours if a new user starts sending spam or engaging in other malicious activities: anti-fraud systems detect such activity instantly. Even a dedicated clean IP is not immune to compromise: if your own account is banned for violations, that IP will end up on the platform's internal blacklists. Therefore, IP monitoring must be regular.
The price depends directly on the type and rarity of the address: from $1.5–$4 per month for a static IPv4 from providers to $70+ per day for premium residential proxies. If the price is suspiciously low, the IP has likely already been flagged in databases or belongs to a shared pool with all the ensuing consequences. Investing in a high-quality IP is a budget safeguard that pays off through account longevity and zero downtime.
The optimal frequency is before every new task (account registration, verification, launching ad campaigns) and at least once every 2-3 weeks for active IPs that are constantly in use. If you use a proxy pool or dynamic addresses, you need to check not only the specific IP but also the entire range—the whole pool can get blacklisted in an instant. Implementing our regular 5-step verification algorithm will help you weed out compromised addresses in time before they lead to mass bans.

